Summary – If you have a virtual private network (VPN) or are planning to get one, you need to understand protocols.
Protocols affect your VPN’s security, speed, and privacy as well as determining what your VPN is best configured for (streaming, torrenting, etc.).
There are five major/widely used protocols for VPNs, OpenVPN, PPTP, L2TP/IPsec, SSTP, and IKEv2/IPSec which each have their own pros and cons.
In this article we’ll discuss the five major VPN protocols, explaining how each protocol works, what activities it is best configured for, and what the pros and cons are.
Before we jump into the particular protocols, though, we need to understand how protocols work in general and why they are necessary.
VPN Protocols 101
Virtual private networks are used to allow remote connection to a private network, in cases of off-site work for a company or as a buffer to the internet.
For the context of this article, we are focusing on those who use VPNs as individuals, as well as those using a VPN as a buffer for their company’s security.
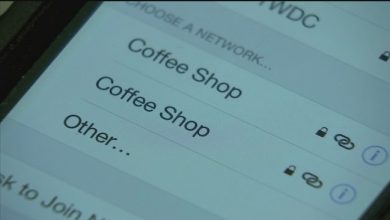
When you go online without a virtual private network, your computer connects to a website requesting the content of the page you are trying to view and then receives that data, be it text, images, downloading files, or streaming audio/video.
Your computer is exposed to whatever content is on that website, including malware, and your computer’s IP address is made available to the website’s server.
This can make your computer vulnerable to malware or hacking as well as making your web activity public.
When you use a VPN, your computer accesses the VPN directly which then accesses the website to request the content of the page.
That content is sent to the VPN server and then redirected to your computer.
The act of routing all the communication between your computer and the web page allows security measures to be put in place to protect you from malware and hacking.
The VPN’s IP address is what is visible to the website (and possibly others), keeping your IP and personal information private.
The security and privacy measures in place on the VPN which protect you are the protocols which we are about to discuss.
Some of these protocols prioritize speed, while others prioritize security and privacy. Typically, there is a trade-off between speed and security/privacy, as these security and privacy measures require extra computing steps as well as time.
Before going into further detail, here’s an abbreviated VPN protocol comparison:
VPN Protocol Comparison (Pros & Cons)
| VPN Protocol | Pros | Cons |
|---|---|---|
| OpenVPN | ||
| IKEv2/IPSec | ||
| L2TP/IPsec | ||
| PPTP | ||
| SSTP |
What VPN Protocol to use, and when?
| VPN Protocol | Unblocks Restricted Sites | Fast Speed (for streaming) | Privacy | Easy Set up |
|---|---|---|---|---|
| OpenVPN | ✓ | ✓ | ✓ | ☓ |
| IKEv2/IPSec | ☓ | ✓ | ☓ | ✓ |
| L2TP/IPsec | ☓ | ☓ | ☓ | ✓ |
| PPTP | ✓ | ✓ | ☓ | ✓ |
| SSTP | ☓ | ✓ | ✓ | ✓ |
From our analysis, here are our recommendations for which Protocol you should use at which instances:
Best VPN Protocol For Streaming – Best choice is to use OpenVPN, IKEv2 or PPTP.
For streaming, you should look for speed first of all.
OpenVPN and PPTP are the fastest protocols, which will guarantee maximum speed for your streaming.
The PPTP and IKEv2 protocols are faster than OpenVPN, but If you want to stream content that is blocked to you, OpenVPN will serve you better, as it would be able to circumvent most blocks, where an IKEv2 or PPTP protocols may not be as successful.
This of course, also depends on the VPN service itself, and its own proprietary methods to unblock websites.
Best VPN Protocol for Torrents – for Torrenting you should look at Privacy first and speed second.
For this reason, we recommend using either OpenVPN or SSTP protocols.
While both offer good privacy and security protection, OpenVPN is faster than an SSTP protocol which is why you should choose as your default VPN protocol for torrenting.
Best VPN Protocol for Privacy – We recommend going with an SSTP or L2TP/IPsec protocols for maximum privacy protection.
Since most VPN services do not provide the SSTP protocol (only ExpressVPN and PureVPN do), L2TP/IPsec would be the most prevalent and recommended choice.
VPN Protocols supported by VPN services
| ExpressVPN | CyberGhost | Ivacy | NordVPN | PrivateVPN | IPVanish | VyprVPN | SaferVPN | PureVPN | HideMyAss | ZenMate | |
| Open VPN (UDP/TCP) | + | + | + | + | + | + | - | - | + | + | - |
| PPTP | + | + | + | + | + | + | + | + | + | + | - |
| SSTP | + | - | + | - | - | - | - | - | + | - | - |
| L2TP/IPSec | + | + | + | + | + | + | + | + | + | + | + |
| IKEv2 | - | - | + | + | + | + | + | + | + | - | + |
OpenVPN
OpenVPN is one of the most widely used and highly secure protocols available to users.
Individuals have the option to use and set up OpenVPN for Mac, OpenVPN for Android, and OpenVPN for Windows, providing a needed level of convenience.
The “Open” part of the name refers to how OpenVPN utilizes open source code, which means the source code is openly available for anyone to access and develop.
An active community has formed around the OpenVPN project, which has kept it up-to-date and provided regular security audits to ensure it’s viability.
OpenVPN is particularly known for its security and privacy as well as it’s adjustability.
The settings made available by your OpenVPN client may vary, but OpenVPN typically works on any port and has five encryption algorithms to choose from depending on the level of security and speed you want.
For the best security and privacy, you should use AES 256-bit encryption, which is essentially unbreakable and should also use a TCP 443 port.
The TCP 443 port will make your connection similar to an https connection, which prevents blocking and can help you bypass censorship.
For greater speed, we recommend using UDP ports, and you can select the default, Blowfish-128 cipher. This isn’t the absolute highest level of security, but for most people, it will suffice and will operate significantly faster than AES 256 on TCP.
What is OpenVPN Most Useful For?
- Activities where you need high security or true privacy
- Just about anything, depending on your setup (you may need to set up for speed and decrease security/privacy for streaming or to speed up torrenting.
OpenVPN Pros & Cons
Pros:
- Very secure
- Flexible in its setup
- Widely available
- Reasonably fast when set up for speed
- Can bypass firewalls
- Open source and regularly maintained
- There is no evidence OpenVPN has been compromised
Cons:
- When set up for high security, it can affect connection speed
- Depending on the setup process of the VPN, setting up OpenVPN can get technical
IKEv2/IPSec
IKEv2 stands for Internet Key Exchange version 2, and is typically paired with IPSec to provide for authentication and encryption.
It was developed by a partnership between Windows and Cisco and primarily configured for working in Windows, though there are versions which can work with other platforms.
In fact, if you use Blackberry, it’s one of the only VPN protocols available.
IKEv2 can maintain a VPN connection even when switching between VPNs or if you temporarily lose your internet connection for an added level of privacy.
It’s a stable protocol that is relatively easy to set up and tends to be fast with low latency.
Unfortunately, there is some evidence that the NSA is using vulnerabilities in IKEv2 to compromise IPsec to track people’s internet activity.
What is IKEv2/IPSec Most Useful For?
- Use with mobile devices
- Use with a Blackberry
- Stable, secure connections when privacy from authorities isn’t a concern
IKEv2/IPSec Pros & Cons
Pros:
- Provides a stable connection
- Fast / Low latency
- Particularly suitable for mobile devices, especially Blackberry
- Easy to set up
Cons:
- Not widely available
- Developed and maintained by Microsoft possibly making it vulnerable to government snooping if Microsoft allows it
- Evidence of NSA snooping already exists
L2TP/IPsec
L2TP stands for Layer 2 Tunnel Protocol which uses a process called double encapsulation for additional security, the first encapsulation establishing a PPP connection and the second incorporating an IPsec encryption.
The protocol doesn’t actually have any encryption; rather it is usually paired with IPsec for the encryption and additional protections IPsec offers.
L2TP only uses UDP ports, which are faster but much easier to be blocked by firewalls, thus making it less effective for getting around censorship.
L2TP is compatible with AES 256-bit encryption; however, this will affect your speed as is true for any protocol (going from 128 to 256-bit encryption is always more secure, but is also always slower).
This protocol tends to be faster than OpenVPN; however, as with IKEv2, because L2TP uses IPsec, there is evidence that the NSA has compromised the protocol.
What is L2TP/IPsec Most Useful For?
- Streaming content
L2TP/IPsec Pros & Cons
Pros:
- Widely available
- Capable of a high level of security
- One of the faster protocols available
- Easy setup
Cons:
- Can be blocked by firewalls
- May have been compromised by the NSA
PPTP
The Point to Point Tunneling Protocol was first used back in 1995, making it one of the oldest protocols still available.
As it’s age may imply, it is also one of the least secure protocols available, as multiple weaknesses have allowed it to be cracked by governments and hackers alike.
Where PPTP shines is in its speed, as it tends to be the fastest protocol available for any VPN.
When speed is the only concern, PPTP may be a good choice, especially if you want to watch something on Netflix which is geographically blocked but is available in other parts of the world.
In those situations, a user isn’t usually concerned about Netflix sending malware or trying to compromise your system; you’re simply seeking to unblock Netflix and watch without buffering interruptions.
What is PPTP Most Useful For?
- Streaming geographically blocked content
PPTP Pros & Cons
Pros:
- Fast connections
- Easy to set up
Cons:
- Not secure
- Does not offer adequate privacy
SSTP
SSTP (Secure Socket Tunneling Protocol) was developed by Microsoft and released with Windows Vista and provides a fast, stable, and secure protocol which is sufficient for most activities.
It uses SSL 3.0 which is reasonably secure, though at this point has been deprecated by the IETF (Internet Engineering Task Force) after numerous attacks were found to be successful against it.
It’s possible that Microsoft has addressed these vulnerabilities, but since the code is proprietary, no one can be sure.
The fact that SSTP was developed and is maintained by Microsoft is either positive or negative, depending on how you look at it.
Microsoft has plenty of resources to maintain the protocol; however, there are also rumors that Microsoft has worked with the NSA to provide backdoor access, thus limiting the privacy SSTP affords you.
What is SSTP Most Useful For?
- Just about anything, so long as you aren’t concerned about the NSA
SSTP Pros & Cons
Pros:
- Stable connections
- Fast with low latency
- Easy to set up
Cons:
- May be vulnerable to attack
- Maybe compromised by the NSA
Bottom Line
The protocols we’ve covered in this article are the most common VPN protocols you will find, regardless of the VPN client you use.
They all have their strengths and weaknesses; however, one stands out above the rest and that’s OpenVPN.
OpenVPN is widely regarded as the safest and most versatile VPN protocol, and it is available with nearly every virtual private network provider on the market.
If you need high security or privacy, the OpenVPN protocol can definitely provide.
If you need speed, OpenVPN may not be the fastest out there, but because of its many configuration options, you can trade a small amount of security/privacy to get the speed you need.
My recommendation would be to start with OpenVPN and use the more secure settings, adjusting the configuration to be faster depending on your needs.
If, after configuring OpenVPN for speed, you find it’s still too slow, then look into another protocol like IKEv2 or SSTP.
If all you want to do is watch geographically blocked Netflix or Hulu content, then maybe try PPTP.
All premium VPN services support OpenVPN and most other VPN protocols as well. Feel free to read more about the best VPN services, how they rank and why we recommend each one of them.
What protocol do you use and why?
Leave a comment below.