Privacy & Cybersecurity
Data Encryption: The Main Things That Everyone Should Know

Summary – Encryption of data is a well-known and quite an understandable process.
Two parties use special encryption and decryption keys. Even if data is intercepted by an intruder during the transferring process from the sender to the recipient, it is impossible to read it without encryption keys. Thus, the interception of encrypted information becomes meaningless.
As you can understand, even though encryption as an idea is simple, it is quite difficult to actually implement the plan.
Encryption, like a medal, has two sides.
Constantly using super-complex data encryption that cannot be cracked is not advisable because it creates great difficulties for the recipient.
If data encryption is performed using too simple encryption keys, it is also at risk: there is a lot of effort and little sense – in such case, it is easier to avoid encryption at all.
Everyone understands that any good system must be balanced.
Data encryption is no exception: information and data should be sent quickly but yet remain secure.
Nowadays, a virtual private network VPN that uses data encryption is a good example of a fast and secure Internet connection.
VPN mainly deals with identifying weaknesses in the security of an Internet user and masking the IP address of large numbers of people.
Premium VPN providers, like ExpressVPN or Cyberghost, pay maximum attention to the comprehensive user security, and not only to connection hacking.
Fortunately, top-notch professionals who use data encryption to protect your information usually have so many options that it is much easier for an attacker to back off.
Data encryption is not an invention of the present time, it is, in fact, older than writing, but with the advent of hardware, the codes are getting more and more complex.
Obviously, the processors used to crack these codes have also become more powerful.
But as professionals say, the weak point of encryption is rarely the code itself, most often that is people at both ends of the connection.
If a person in possession of the key is an attacker planning to steal information, there is no code in the world that can withstand this very attack.
What is Data Encryption?
Simply put, data encryption is about modifying information to make it unrecognizable to outsiders.
Typically, data is encrypted using some form of encryption or encryption key (password) that is known only to two parties: the sender and the recipient.
Digital data encryption is more complex than handwritten encryption though based on the same principles.
There are two types of encryption, each using different methods of encrypting and decrypting information.
The most common type is symmetric data encryption which assumes that the sender and intended recipient use the same key to encrypt and decrypt the message.
Another, more complex type of data encryption is called asymmetric. In this case, the sender and the recipient use different keys to encrypt and decrypt the message.
Data encryption converts the transmitted information into a bunch of incoherent characters that are impossible for a random stranger to read and understand.
Only a person with a decryption key can recognize this information.
Since most data, including media, is displayed in text form, they can be encrypted in the same way.
Encryption of data ensures the confidentiality of all its types.
Finally, one thing needs to be understood – encrypting data is a rather complex intellectual task.
Movies often show us nosy secret agents reading encrypted messages with a glass of martini in one hand and a gun in the other.
In fact, the people encrypting data are rarely sharpshooters.
Quite often, though, they are talented mathematicians able to come up with codes, algorithms, and encryption keys to ensure that every user has secure encryption that can withstand any kind of attack.
The average user receives an off-the-shelf product in the form of special apps.
Data Encryption. Stages of Development
At all times, having the right information has provided great strength and a significant advantage.
The winner is one who knows more than his enemy.
Before writing, people encrypted information with gestures and sounds.
Military leaders used complex horn signals to make sure that the enemy did not understand what was going to be done against them.
There were special people on the enemy side trying to recognize these signals and understand what was going on before it was too late.
One of the original encrypting methods of the antiquity period is a permutation code.
Most people are familiar with this type of encryption where data is encrypted by shifting the alphabet letters.
It’s a very simple, but functional, symmetric encryption.
Over time, encryption and cryptanalysis have become increasingly common, and the encryption process – much more complex.
At one point, the effectiveness of using the letters to encrypt messages was exhausted, and people turned to math.
Simple computation has become advanced mathematics, then irrational mathematics, and now it has reached a point where the letters prevail again in these calculations but represent other, equally complex calculations.
What is Data Encryption for Today?
In order to understand that, we need to figure out who can hunt down our personal data.
It could be government officials who want to know as much as possible about their citizens for national security purposes, it could be corporate managers who dream of getting hold of the secrets of their competitors, or it could be a gifted hacker from some provincial town stealing credit card information just to prove that he can do it.
Information of national importance is protected by special services with highly qualified staff, but who or what protects yours?
Some people think they don’t need antivirus or VPN connection because they don’t know the important secret information.
This is a big mistake.
Your personal data is very important information. If it falls into the hands of an attacker, it may get you in deep trouble.
Even if you don’t keep a good deal of money on your bank account, you may have a good credit history.
The danger is that by taking possession of your account details, the intruder can get a loan using your name, which you will have to repay or go to court and try to prove that you have nothing to do with it.
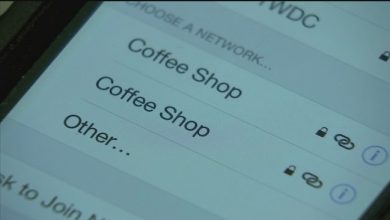
It is possible that no one will purposefully hunt down precisely your personal data, but if it is easily accessible, there is a high probability that you will be attacked earlier than someone else who goes online anonymously through an encrypted VPN tunnel.
Bottom Line
It is not a new idea, but unlike in the past, when it was only necessary for kings and army generals, data encryption is now very important for all members of society, including children and adults.
We all produce, post a lot of private information on the Internet every day, that’s why we need to ensure its proper security.
There is no need to be afraid of using any service on the Internet, we just need to take some actions to protect ourselves.
Using a VPN to mask your IP address and connect your devices to the Internet through an encrypted VPN tunnel is one of the best ways to provide individual protection against hacking and attacks.
Remember that all of your confidential information must be securely encrypted, and each of us should be careful online to not provide information that must remain confidential.
If you combine 256-bit data encryption with common sense, your browsing experience will be secure and enjoyable.